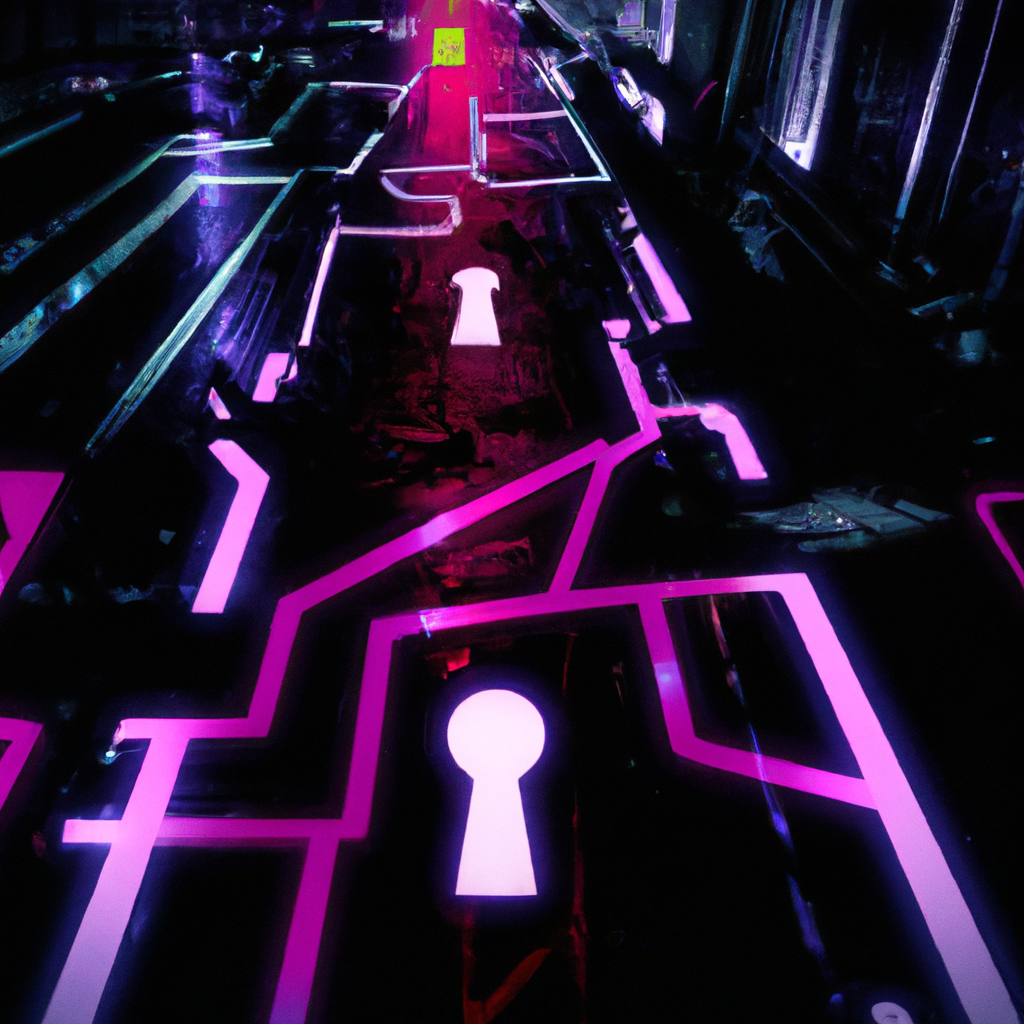
You punch through darkness as rain-slapped neon reflections trickle down cracked pavement. Rain-cooled circuits thrum under synthetic sky lanterns, light bending against chrome, the city breathing with data. In this neon cathedral you are both worshipper and sacrificial lamb. The firewall stands ahead, an invisible fortress of digital flame, blinking sentinel nodes and packets in constant combat, energy pulses humming like a heartbeat gone haywire. You taste the ozone, programming languages bitter, every line of code a key, every flaw a door left ajar.
You are awake in the network, aware of proxies, ports, signatures. Every ping, every handshake, every dropped packet echoes accusation. The firewall is the threshold between order and chaos, between what the system allows and what it fears. In this landscape you seek knowledge, edge, control; you study the glowing grids, decompile the whispered protocols, track the hidden backdoors. If you want to learn how to hit the firewall, to probe its defences, to understand its guts, you must first see it, palpably, as both beast and guard.
Hitting the Firewall: What It Means and Why It Matters
“Hitting the firewall” is not just an assault; it is a reconnaissance, a dialogue of shadows. It means probing, testing, understanding where the fortress might fracture, be it in misconfigured rules, forgotten open ports, or weak authentication. In the hands of a defender it is preemptive hardening; in the hands of an attacker it is exploitation. As a cybersecurity newbie you will play both roles: probing your own systems first to protect, before you ever think of stepping across legal lines.
You need to grasp:
- Packet filtering versus stateful inspection, application-level proxies, deep packet inspection, that tapestry of firewall technologies.
- Rule ordering and implicit denies: the top rule might never fire if earlier allow rules swallow the traffic.
- Default configurations: often the most vulnerable, because they favour ease over security.
Practical Tools and First Steps
Here are actionable techniques you can try safely, on your own lab environment. Always ensure you have explicit permission before probing any system you do not own.
Port scanning with nmap (on your own machine)
bash
# Scan common ports on localhost
nmap -sS -sV 127.0.0.1
# Scan a target IP on specific port range
nmap -p 1-65535 -T4 --open example.com
-sSperforms a TCP SYN stealth scan, less likely to be logged.-sVattempts version detection.
These scans help you discover open ports and services that your firewall is letting through. Use in your personal lab or authorised test networks only. Misuse could be deemed illegal.
Testing firewall rules with Python
Here is a simple Python script that attempts TCP connections to a list of ports, to test whether the firewall allows or blocks them:
python
import socket
target = '192.168.1.100' # change to your lab machine
ports = [22, 80, 443, 8080, 3306]
for port in ports:
sock = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
sock.settimeout(1)
try:
result = sock.connect_ex((target, port))
if result == 0:
print(f'Port {port} is OPEN on {target}')
else:
print(f'Port {port} is CLOSED or FILTERED on {target}')
except Exception as e:
print(f'Error checking port {port}: {e}')
finally:
sock.close()
Warning: this script could be considered intrusive on networks you do not own; do not use it against external targets without authorisation.
Inside Firewall Configurations
You must read configs like archaeologists read runes. Most firewalls, whether iptables, UFW, Windows Firewall, or enterprise-class systems, have rulesets, zones, chains.
Using iptables (Linux)
bash
# Show current rules
sudo iptables -L -v -n
# Basic rule: block incoming HTTP
sudo iptables -A INPUT -p tcp --dport 80 -j DROP
# Allow SSH from a particular network
sudo iptables -A INPUT -p tcp -s 10.0.0.0/24 --dport 22 -j ACCEPT
Understand the order: earlier rules evaluated first. Unmatched packets fall to final policy, often “DROP” or “ACCEPT”. Always test connectivity via console before applying because you might lock yourself out.
Windows PowerShell: Modifying firewall policy
powershell
# List current firewall rules
Get-NetFirewallRule | Where-Object { $_.Enabled -eq 'True' }
# Block inbound HTTP
New-NetFirewallRule -DisplayName "Block HTTP Inbound" -Direction Inbound -Action Block -Protocol TCP -LocalPort 80
# Allow outbound DNS
New-NetFirewallRule -DisplayName "Allow DNS Outbound" -Direction Outbound -Action Allow -Protocol UDP -RemotePort 53
Use caution manipulating firewall rules on systems in production; misconfiguration can open vulnerabilities or disrupt services.
Recognising and Exploiting Weaknesses
To “hit the firewall” effectively you must follow its trail of cracks:
- Unused default rules and legacy entries, often allow more than you expect.
- Weak or no logging: if there is no visibility, breaches go unnoticed. Ensure logs are enabled, stored securely, rotated.
- Firewall bypass via VPN or proxy chains. Attackers may tunnel through allowed protocols.
- Application-layer attacks: rules might permit HTTP traffic but not inspect payloads, allowing injection or cross-site scripting.
Defensive Strategies
If your goal is to build defences rather than break them, these are essential:
- Principle of least privilege: allow only what is necessary.
- Centralised rule management, version control of firewall configuration.
- Regular audits: test old rules, remove what’s obsolete.
- Employ Intrusion Detection Systems (IDS) to monitor what the firewall allows.
- Segmentation: limit broad access between network zones.
Getting Ready to Break Through Firewalls
Aim
You will learn how attackers evade or bypass firewalls using practical techniques so that you understand both how firewalls operate and how to test or defend them effectively.
Learning Outcomes
By the end of this guide you will be able to:
- recognise common firewall and IDS/IPS evasion methods (packet fragmentation, source-port spoofing, stealth scanning) (techtarget.com)
- carry out Nmap scans that disguise or mislead firewall rules (using decoys, spoofed source ports, custom packet flags) (pluralsight.com)
- script simple bypass attempts in Bash or Python to test firewall weaknesses practically
- analyse firewall logs or network traffic to detect possible evasion attempts
Prerequisites
You will need:
- a Linux machine or virtual machine (e.g. Kali Linux or Ubuntu) with root or sudo access
- Nmap installed for port scanning (pluralsight.com)
- Python (3.x) for scripting custom probes
- basic knowledge of TCP/IP, ports, flags (SYN, ACK, etc.), basic networking and firewall concepts
- a test network or lab environment where you have permission to run scans and bypass tests
Step-by-Step Guide to Hitting the Firewall
- Map open ports with simple scans
Begin with standard scans to understand firewall behaviour:
Bash:
bash
sudo nmap -sS -p 1-65535 <target_ip>
This reveals which ports are open, filtered or closed. Observe how many ports appear filtered.
- Switch to stealth or alternative scan types
Use packet-flag variations or custom scan types to see if firewall filters change behaviour:
bash
sudo nmap -sA -sU -Pn -p 1-1000 <target_ip>
-sA (ACK scan) or -sU (UDP) may pass where SYN scans are blocked. -Pn skips host discovery.
- Use decoys and source-port spoofing
To confuse firewall rules or IDS, use decoys or spoof the source port:
bash
sudo nmap -sS -p 80,443 <target_ip> --source-port 53 -D RND:10
Decoys (-D) hide your real IP among others. Source-port 53 mimics DNS traffic. (reddit.com)
- Fragment packets to evade packet inspection
Firewalls or IDS may drop or ignore fragmented traffic. Use Nmap’s fragmentation option:
bash
sudo nmap -sS -f <target_ip>
Or craft fragmented packets in Python using scapy:
python
from scapy.all import IP, TCP, fragment, send
p = IP(dst="<target_ip>")/TCP(dport=80, flags="S")
frags = fragment(p, fragsize=16)
for f in frags:
send(f)
- Probe with application-level traffic over allowed services
If only HTTP (port 80/443) is allowed, send private data or reverse shells through HTTP or TLS tunnels. For example using “curl” for HTTP POST:
bash
curl -X POST -d "data=attack_payload" http://<target_ip>/allowed_path
- Review logs and traffic to detect evasion attempts
On the firewall or IDS, examine log entries that show:
- fragmented packet streams or dropped fragments
- unusual source ports (e.g., high numbers or standard service ports used for non-standard traffic)
- high numbers of filtered or dropped SYN-ACK or UDP probes
UsetcpdumporWiresharkto monitor. For example:
bash
sudo tcpdump -i any host <target_ip> and (tcp[13] & 0x02 != 0)
This captures TCP packets with the SYN flag set.
Practical Code Snippets Summary
- Bash Nmap stealth scan with decoys
bash
sudo nmap -sS -p 22,80,443 <target_ip> --source-port 53 -D RND:5
- Python fragmentation script using Scapy
python
from scapy.all import IP, TCP, fragment, send
tgt = "192.168.1.10"
pkt = IP(dst=tgt)/TCP(dport=22, flags="S")
for frag in fragment(pkt, fragsize=24):
send(frag)
- Detecting SYN packets via tcpdump
bash
sudo tcpdump -n -i any tcp[tcpflags] & tcp-syn != 0 and dst host <your_firewall_ip>
Follow these steps in order, practising each method in a safe lab environment. By doing so you will understand both offensive techniques and defensive detection methods.
At the edge of circuits, where packets hiss and lights bleed into darkness, hitting the firewall is both art and science. You will mess up, break things, maybe even fry your own network. But you will learn. You will see how the fortress stands, where it is weakest, how you might defend or, in other contexts, exploit. Step into this neon storm, code in hand, questions burning, this is where your journey begins.